Hi, I'm Cale.
A human that writes code
Projects

The Last of Us Part II Remastered
My third triple-A title credit at Naughty Dog. I worked on tools that helped build, test, and report on player telemetry post-launch.
The Last Of Us Part 1
My second AAA credit at Naughty Dog! I worked behind the scenes on the core tech team developing software to improve development and testing workflows. I also worked on engine code to assist QA with performance analysis and instrumented game analytics for Sony.
Uncharted: Legacy of Thieves Collection
My first real AAA credit at Naughty Dog! I worked behind the scenes on the core tech team developing software to improve development and testing workflows.
Financial Inclusion Insights Website and Data Tool
Column Five collaborated with InterMedia, which created the Financial Inclusion Insights (FII) Program in 2013, in partnership with the Bill and Melinda Gates Foundation. The FII program was created to collect and analyze meaningful data on financial behaviors in eight countries across Africa and Asia.
Groove Glider
Groove Glider is an experimental side-scroller that leverages the dynamic game state to influence the in-game music. Created by Column Five on the Quintus HTML5 game engine.
Tapad Identity Visualization
Interactive, audience-specific sales narrative with a gated, data-driven visualization.
Place Goldblum
Placeholder image service similar to Fill Murray, Placecage, etc. but with photos of Jeff Goldblum instead.

GDIS & MMIST
Immersive training simulator prototype for the US Army using commercially available hardware and software.

Firearms: Source
A Source Engine (Half-Life 2) total-conversion developed in C and C++ using the Source SDK.
EggTrack
A project created while working at Column Five for Compassion in World Farming to make cage free egg data for global companies easily understandable.
Timios, Inc. Website
Timios asked Column Five to re-brand and re-create their corporate website as well as update their existing Closing Cost Calculator and Net Sheet Calculator appearance.

Firearms
A GoldSrc Engine (Half-Life 1) total-conversion developed in C and C++ using the GoldSrc SDK.
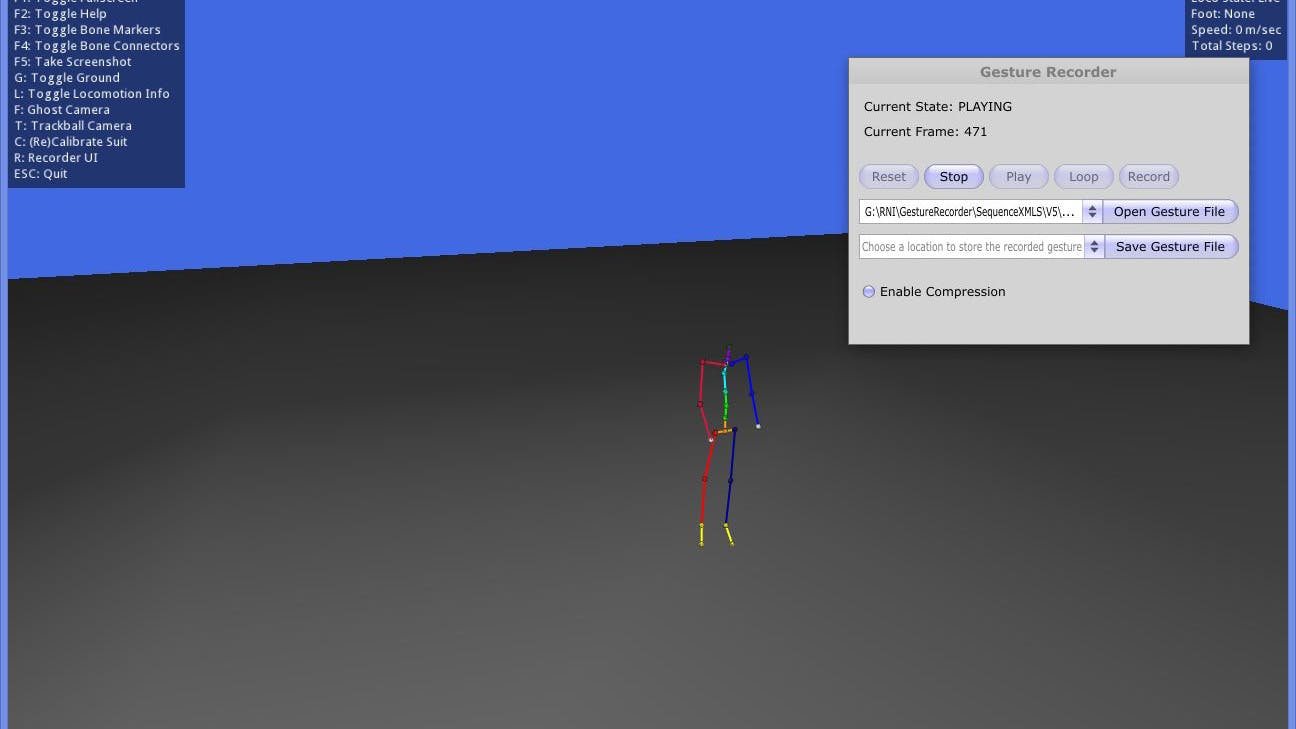
VIKENG Mocap Tool
Native application used to record and review motion capture data as well as gesture recognition information.
Mashable: Something's Got to GIF
Column Five partnered with Mashable to create an interactive survey to ask readers how they pronounce various tech terms. The interactive was a huge success, with more than 29,000 responses from 191 countries.
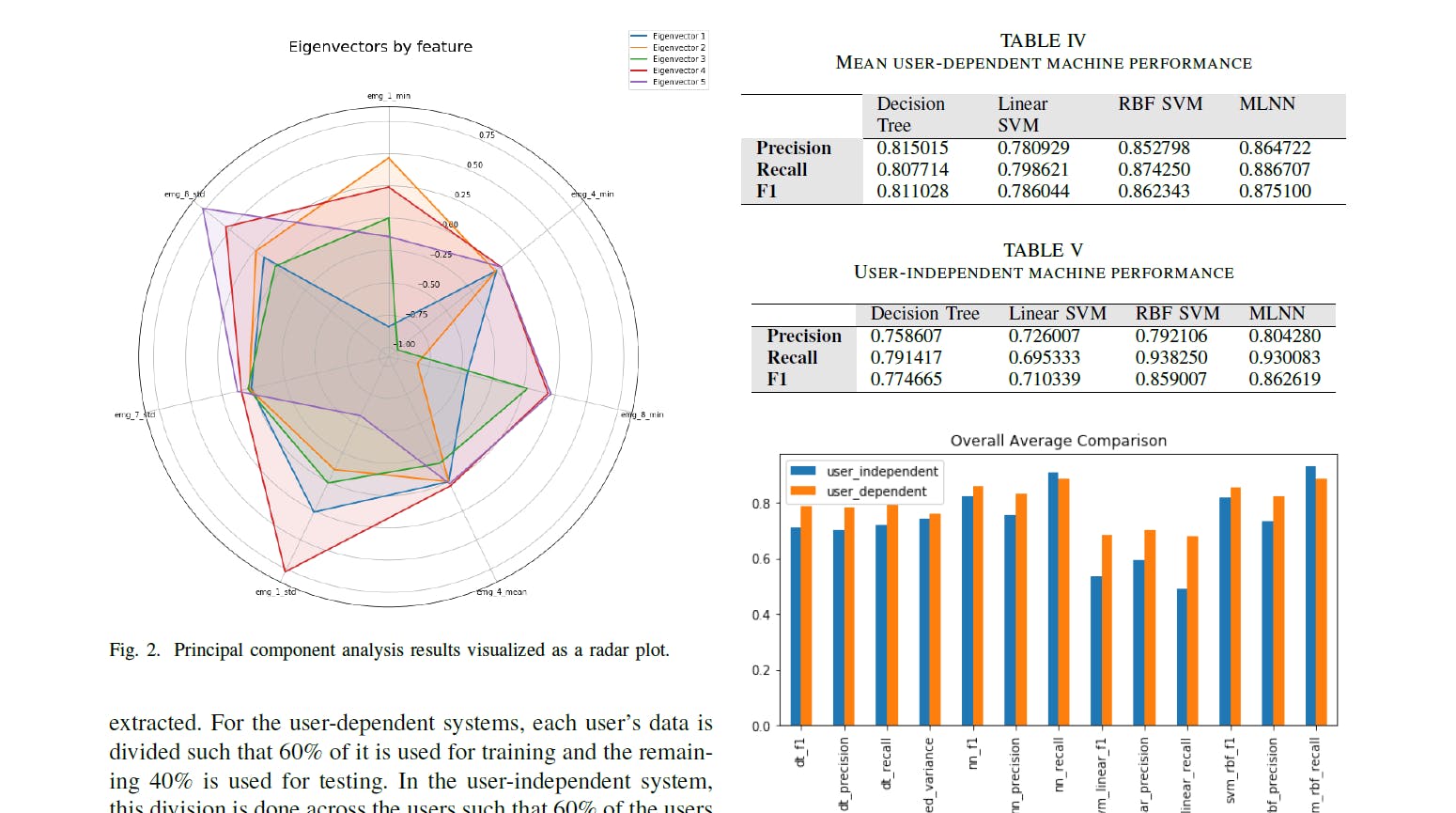
Using Machine Learning to Detect Eating Activity in Electromyography Data
While enrolled at Arizona State University, one of our class projects was to utilize raw Electromyography data from the dominant hand of a number of users and detect at what points those users were eating versus doing something else.
Skoll Global Threats Fund Community Map
Column Five partnered with the Skoll Global Threats Fund to design and develop a dynamic and thoughtfully built community of practice website for EndingPandemics.org.
Microsoft's Anatomy of a Breach
This HTML native site analyses the various stages of a company security breach from the hacker’s POV. Highlighting the systemic weaknesses hackers look for most, the site presents Microsoft’s solutions to avoiding and overcoming such gaps in security.

Firearms 2
Between Firearms and Firearms: Source there was Firearms 2. This was one of at least two attempts at a Firearms reboot.